My home setup consists of a Linksys WRT-54GL wireless access point connected to a high-bandwidth internet connection. The Linksys WRT-54GL is version 4 of the WRT-54G. With version 5 of the WRT-54G Linksys changed the hardware and stopped using Linux internally. Because of these changes the device could no longer run third-party firmwares. The WRT-54GL is Linksys' response to hobbyists (hackers) who still want to tinker with other firmwares. For this tutorial you'll need a router capable of running the DD-WRT firmware. This excellent firmware has many great features including an SSH daemon which is a prerequisite for our tunneling. A list of supported devices can be found here.
Instructions for flashing the firmware can be found all over the Internet. I'll assume the reader can flash the router and get the DD-WRT firmware running (Administration->Firmware Upload). Some Linksys routers (including the WRT-54GL) have a 3MB limit to firmware size so if that is the case use the mini version of DD-WRT first, once that is running upload the version you want.
I'm using DynDNS to keep tabs on my dynamic Internet IP address. This free service allows you to keep your changing IP address up to date and matched to a hostname. DD-WRT has support for automatically keeping the address updated. Other services are supported too so you can choose your favorite. Once your dynamic DNS account is created you can enter the relevant information into the Setup->DDNS tab in DD-WRT.
The next thing you will need to do is enable the SSH daemon. This can be done throughout the Administration->Services tab in DD-WRT. Under SSHD select enable. The login will be username:root password:[your router password]
To connect to the SSH server and tunnel HTTP you will need the Putty SSH client. To connect to your router enter the hostname or IP address of your router on the Session tab:

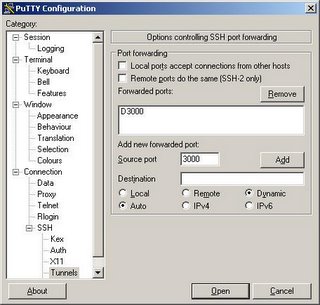
Next, to setup the tunnel click on Tunnels, enter 3000 (or whatever local port you'd like to use) for the source port, click Dynamic and click Add. This will create a SOCKS proxy on your local machine on port 3000 (or whatever port your chose) that you can use with your web browser.
Now you can click Open to log into your router. The tunnel isn't created until you log in. Remember that your username is root and your password is your router password (you changed it right?).
Now you're ready to connect your web browser. Using Firefox, you will have to configure a proxy server. Click Tools->Options. Then under General click Connection Settings. On this screen you can configure the SOCKS proxy that you've set up using Putty. Select Manual proxy configuration, enter localhost for the SOCKS host and 3000 for the port (or whatever you used). Click OK. You should now be tunneling through your home router over ssh.

You can verify that the connections are being forwarded by looking at the Putty Event Log. You should see something similar to the following after loading www.google.com in your web browser.

47 comments:
Now all you have to do is explain how to edit the config file so you can tunnel from the outside in.
Sniper,you are certainly correct about the DNS requests. There was a similar comment and reply from me in the Digg comments. I targeted this tutorial at legitimate uses where you're more concerned about conceling the content you're browsing for not where you're browsing. This has uses as public internet access spots too such as libraries and hotspots. It could also be used if you cannot go outbound on 443 (but 23 is allowed) which would prevent you from connecting to HTTPS sites. My mistake was thinking that people on the internet do something other than download porn.
You don't need to have a computer running continuously at home. Just the router (which is a computer)...
The DNS servers you use are configured in your TCP/IP settings (if you're using Windows). The server's to use can come from your DHCP server or you can specify them yourself. There are a bunch of public DNS servers that you can use (4.2.2.2, and 4.2.2.6 are pretty fast)... Search and you shall recieve...
Wonderful article, very well explained.
Recursive DNS requests going out is definetely a privacy issue. Anyone looking for DNS servers should considering using DynDNS's DNS servers. They are significantly faster than any public ones you will find.
Wow can't wait to try it out. Is there a way to change the port to 21? Our firewall blocks everything but 20-21 and then to get out port 80 you have to use a web proxy.
@sniper + jim
I'm not sure but maybe you could change the dns servers to the ones f http://opendns.com ?
If I am forwarding ssh to my local machine, on port 22, as it is hosting X over SSH, then could I change remote access and web management to different ports?
1984 and 1985?
Then ssh to each port depending on what service I need?
Thanks!
If you install the Firefox plugin FoxyProxy, it has an option to send DNS requests over Socks
Doug - I don't see why not. The nice thing about 22 though is that you can get out of most networks on 22. 1984 and 1985 are not as likely to be let out.
actually qwerty967, that's not quite true (but helpful in my quest for an answer). See what codeblog has to say.
I found one additional "gotcha" with these instructions. I could not get PuTTY to connect to the router externally, I kept getting a ‘Network error: Software caused connection abort’ error.
When I got back home, I tried connecting with PuTTY on one of the LAN ports internally. It worked fine. Once I had done the key setup from inside the router, everything worked great from outside the router from that point on.
CatholicCybrpunk what firmware are you using on your router?? if your using dd-wrt then you need to open up port 22 to the out side world, you need to add the following lines to your firewall.user:
iptables -t nat -A prerouting_rule -i $WAN -p tcp --dport 22 -j ACCEPT
iptables -A input_rule -i $WAN -p tcp --dport 22 -j ACCEPT
replace the port (--dport) with what ever port your using, 443 is a common one for avoiding detection since its the port https (secure http) runs on.
If you don't know how to use putty, I suggest you use a web proxy to surf the Internet. Try this: www.aplusproxy.com
Is there anyway to access an NDAS device I have hooked up to my router from outside my LAN using something like this method?
Is there anyway to access the contents of an NDAS hard drive I have hooked up to my router from outside my home LAN using this method?
Usman, once you create the tunnel you will have full access to your internal network over HTTP. If you can access your internal device over HTTP then you're set. If the device is accessed over a different port you will need to forward that port over SSH and then set up your client application to use the proxy (if it supports upstream proxys).
i discovered this post by coincidence. very great. easy to understand and works smoothly.
didn't know I can do it with my router. Always used another linux box with squid proxy and local port forwarding. now i can turn off my linux box and just use my router (can save electricity).
ad firefox & dns: you don't need foxyproxy to also use socks for dns requests. in fact it's overkill.
you just can enter about:config in the address bar.
and then search for 'dns'.
and set 'network.proxy.socks_remote_dns' to 'true'.
sincerely
ernst
Hello! I don't know anything about networking but I would like to access internet bypassing a restriction imposed by the network administrator on all traffic except that on port 80. But this last one is redirected to an https intranet login page.
Is there any way to encrypt my browser sessions as to not be redirected locally?
I've done everything as you described, and socks forwarding is established (in event: Local port 3000 sock forwarding) but when i try to type www.google.com only blank page displayed.
In event is no record about sock forwarding.
Shedoks, do you have a desktop firewall running? If so, that may be blocking the connection back on port 3000. Other than that I would say check all the settings. Make sure you have used dynamic port forwarding in Putty and make sure your browser's upstream proxy is configured correctly.
This was a great solution for me! I've been paying $10 per month for secure-tunnel which I used at public hotspots. Now I will be using my dd-wrt!
Shedlock, you did the same thing I did. In firefox, on the proxy section, all the entries should be blank, no ftp proxy, http proxy, etc. There should only be an entry for the SOCKS Host, if you followed this tutorial, that will be 127.0.0.1 port 8080.
Writeup really makes us understand every think. Cool information.
Regards,
Komail Noori
Web Site Design - SEO Expert
This setup seem to work fine for me when I open web pages restricted by network admins at work. Had some DNS issues at first. Solved with Chef vom Dienst advice - thank you!
But when I try to open java applets anywhere on the web or make my favourite IM to work (set proxy to 127.0.0.1:8080 in it) it fails.
Any ideas Gentlemen?
cheers!
k
Hi all,
I think the better way is to build up a VPN tunnel from the company PC to the WRT54GL and route one address (proxy.homeip.net) into this tunnel..
.. on the other end, behind the WRT54GL, a proxy server is waiting for data..
The rest you know..
This is completely secured and works just fine ;)
Cheers
Hey Vista Users! I just got this working. The comments here helped me set everything up right except for one little detail:
When setting your proxy in your application (e.g., firefox) you MUST use 127.0.0.1 - "localhost" will not work. I spent hours trying to figure this out.
GREAT, GREAT INFO!!!
I made the config change that Chef vom Dienst mentioned, but how can I verify that it's using my servers DNS.
Help please
Using ddwrt router setup, FoxyProxy.
Im trying to test this from inside the LAN. (Not outside -- I know but I cant go to coffee house to see if setup is running).
From inside the lan I am able to ssh into the router with -D 9999 parameter set.
However whenever I point firefox to use 127.0.0.1 port 9999 as SOCKS 5 proxy, Im getting following error inside my ssh login shell:
channel 2: open failed: connect failed:
does this mean anything? It doesnt work when I do this -- all I get is a blank page in firefox
I got it setup and it seemed to work but I keep getting:
Forwarded port closed
In the putty log. I can still get to websites but I'm also trying to stream some XM music which doesn't seem to work. Any ideas as to what the message could mean?
BlueBeetle: Try enabling TCP keepalives in putty by selecting it on the Connection settings. For the XM thing, are you streaming with the browser? Often, streaming radio will run on a different port so you would have to forward that port too and configure the application to use it.
It looks like the TCP Keep alive worked! Even for the streaming XM. Thanks! w00t!
I had ssh working great yesterday using putty and foxy proxy. My router turned off and on once but data was not reset back to factory defaults. I am using port 443. and can no longer access it externally today. Any ideas?
oh kool this is exactly what i need, is ther a way to get this working with lynksys wag354g i know its a lame router but thats what i have.
oh kool this is exactly what i need, is ther a way to get this working with lynksys wag354g i know its a lame router but thats what i have.
m - I don't think that model will work with DD-WRT. The list of supported devices can be found here http://www.dd-wrt.com/wiki/index.php/Supported_Devices in case you want to buy something else.
when using putty I enter all of the information and then click open.
When i click open I get an error message network error: connection refused. I have checked many times to make sure that I have done all of the steps of the tutorial.
I already installed dd-wrt on my router and just wonder if there is another way using this method without Putty application ? or at least make my router become a web proxy . Thanks!
it is helpfull and working fine. Big thx ;-)
@Shedoks
Ensure that you only have an address in the SOCKS proxy address space - leave the others blank.
It should work after that. If not - I'm sorry I'm of no help.
Tunnelier is a much more comprehensive SSH client than Putty. Lightweight too.
The FoxyProxy add-on for Firefox allows you to send DNS requests through your SOCKS proxy.
I prefer no-ip over DynDNS, but that's just me.
Tunnelier is a much more comprehensive SSH client than Putty. Lightweight too.
The FoxyProxy add-on for Firefox allows you to send DNS requests through your SOCKS proxy. FoxyProxy is NOT overkill, it's very intuitive and flexible enough to match specified patterns to load through the proxy. Such as setting all *://192.168.*.* traffic as a blacklist so if you are accessing LAN services then you most likely don't want to go through your proxy. Since you are already utilizing FoxyProxy's awesome power, why not tick the little option box that says "Send DNS requests through SOCKS". I don't use my SSH Tunnel on all my networks and need it to be disabled at times. So unless you want to go in to about:config and modify the 'network.proxy.socks_remote_dns' to 'true' key EVERY TIME, I strongly suggest FoxyProxy, there's no reason not to use it. At this point you may think I'm getting some kick backs from FoxyProxy, this is not the case, I just believe in this add-on because its powerful flexibility.
I prefer no-ip over DynDNS, but that's just me.
Hi
Is it possible to use this setup with
Privoxy as well? Lets say I am sitting at a cafe and I have privoxy running on my laptop. I want to use privoxy+my router socks proxy, is such thing possible, if so how?
Btw here is another method that does not invole a router(If I understand correctly)
You need to have cygwin installed
C:\cygwin\bin\ssh.exe -ND 9999 your_ssh_username@localhost
Once this is running put 9999 as the socks proxy port number in your browser proxy section.
Does this also works if my company is using an proxy? I have to use our proxy to surf the web...
I have successfully used tunneling from work to my home PC, even with remote desktop through the router.
I am looking for a cheap linksys router with DD-WRT support,
Something I am concerned with is the DNS servers. At my workplace, I have to connect through their proxy server (ccproxy), and the TCP/IP settings are configured to use my work's DNS prefixes...
How will this effect my tunnel, and will my DNS requests be local or remote?
Also, I think on puTTy I saw options to send DNS requests remotely instead?
Your reply is much appreciated.
Great tutorial.
Thanks,
Dan
Does this also works if my company is using an proxy? I have to use our proxy to surf the web design
been running a similar setup myself. Love using my DD-WRT router, purchase a E4200 already flashed at https://www.flashrouters.com.
It can pre-configured and customized to my network setup, pretty convenient.
Excellent post, thanks.
Post a Comment